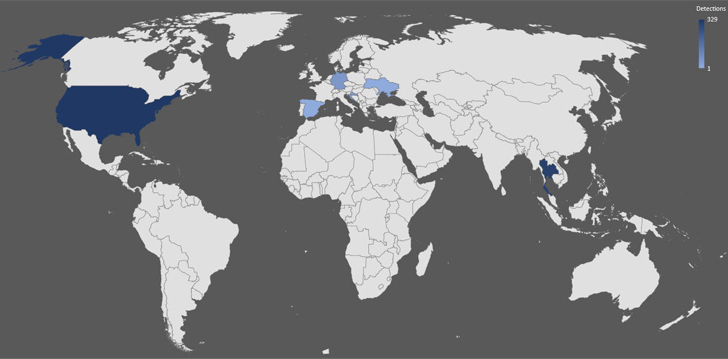
A new Golang-based information stealer called Skuld has compromised Windows systems across Europe, Southeast Asia, and the U.S.
“This new malware strain tries to steal sensitive information from its victims,” Trellix researcher Ernesto Fernández Provecho said in a Tuesday analysis. “To accomplish this task, it searches for data stored in applications such as Discord and web browsers; information from the system and files stored in the victim’s folders.”
Skuld, which shares overlaps with publicly available stealers like Creal Stealer, Luna Grabber, and BlackCap Grabber, is the handiwork of a developer who goes by the online alias Deathined on various social media platforms like GitHub, Twitter, Reddit, and Tumblr.
Also spotted by Trellix is a Telegram group named deathinews, indicating that these online avenues could be used to promote the offering in the future as a service for other threat actors.
The malware, upon execution, checks if it’s running in a virtual environment in an attempt to thwart analysis. It further extracts the list of running processes and compares it against a predefined blocklist. Should any process match with those present in the blocklist, Skuld proceeds to terminate the matched process as opposed to terminating itself.
Besides gathering system metadata, the malware possesses capabilities to harvest cookies and credentials stored in web browsers as well as files present in the Windows user profile folders, including Desktop, Documents, Downloads, Pictures, Music, Videos, and OneDrive.
Artifacts analyzed by Trellix show that it’s engineered to corrupt legitimate files associated with Better Discord and Discord Token Protector and inject JavaScript code into the Discord app to siphon backup codes, mirroring a technique similar to that of another Rust-based infostealer recently documented by Trend Micro.
???? Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
Select samples of Skuld also incorporate a clipper module to alter clipboard content and steal cryptocurrency assets by swapping the wallet addresses, which the cybersecurity company theorized is likely in development.
Data exfiltration is achieved by means of an actor-controlled Discord webhook or the Gofile upload service. In the case of the latter, a reference URL to steal the uploaded ZIP file containing the stolen data is sent to the attacker using the same Discord webhook functionality.
The development points to steady adoption of the Go programming language among threat actors due to its “simplicity, efficiency, and cross-platform compatibility,” thereby making it an attractive vehicle to target multiple operating systems and expand their victim pool.
“Additionally, Golang’s compiled nature lets malware authors produce binary executables that are more challenging to analyze and reverse engineer,” Fernández Provecho noted. “This makes it harder for security researchers and traditional anti-malware solutions to detect and mitigate these threats effectively.”