A new large-scale smishing campaign is targeting the U.S. by sending iMessages from compromised Apple iCloud accounts with an aim to conduct identity theft and financial fraud.
“The Chinese-speaking threat actors behind this campaign are operating a package-tracking text scam sent via iMessage to collect personally identifying information (PII) and payment credentials from victims, in the furtherance of identity theft and credit card fraud,” Resecurity said in an analysis published last week.
The cybercrime group, dubbed Smishing Triad, is also said to be in the business of “fraud-as-a-service,” offering other actors ready-to-use smishing kits via Telegram that cost $200 a month.
These kits impersonate popular postal and delivery services in the U.S, the U.K, Poland, Sweden, Italy, Indonesia, Malaysia, Japan, and other countries.

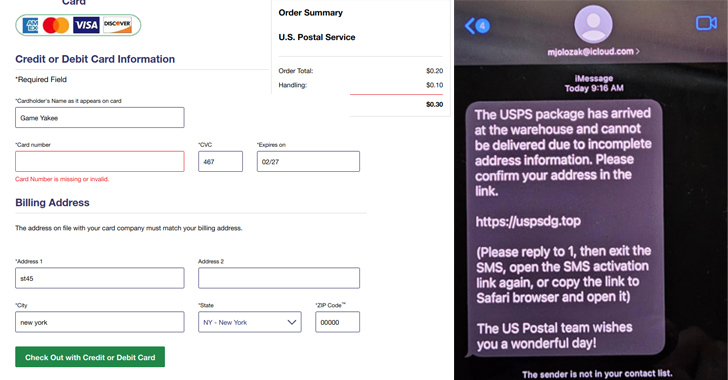
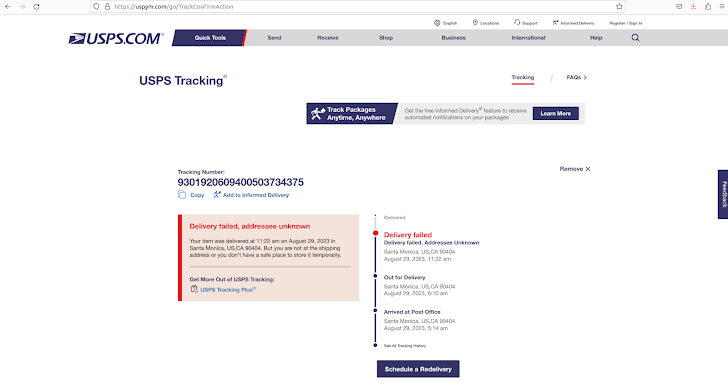
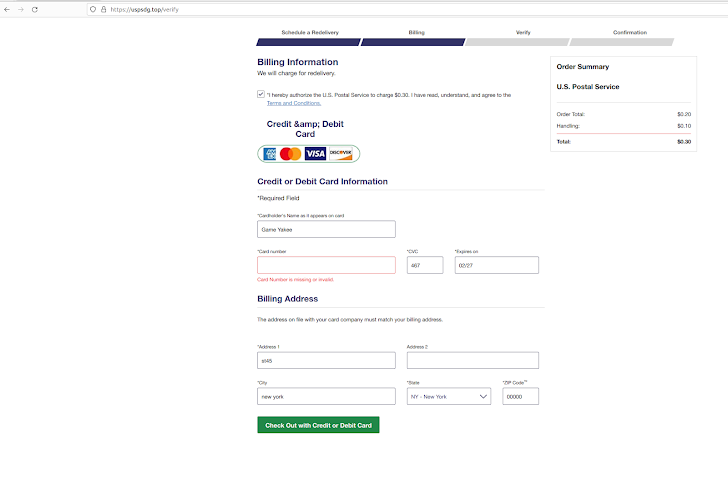
A stand-out aspect of the activity is the use of breached Apple iCloud accounts as a delivery vector to send package delivery failure messages, urging recipients to click on a link to reschedule the delivery and enter their credit card information in a fake form.
Resecurity’s analysis of the smishing kit revealed an SQL injection vulnerability that it said allowed them to retrieve over 108,044 records of victims’ data.
“Considering the identified vulnerability or potential backdoor, it is possible that key members of ‘Smishing Triad’ organized a covert channel to collect results with intercepted personal and payment data from other members and clients leveraging their kit,” the company said.
“Such tradecraft is widely used by cybercriminals in password stealers and phishing kits, allowing them to profit from the activities of their clients, or at least to seamlessly monitor their activity just by logging into an administration panel.”
The Telegram group associated with Smishing Triad includes graphic designers, web developers, and sales people, who oversee the development of high-quality phishing kits as well as their marketing on dark web cybercrime forums.
Detect, Respond, Protect: ITDR and SSPM for Complete SaaS Security
Discover how Identity Threat Detection & Response (ITDR) identifies and mitigates threats with the help of SSPM. Learn how to secure your corporate SaaS applications and protect your data, even after a breach.
Multiple Vietnamese-speaking members of the group have been observed collaborating with the primary threat actors in these efforts, with the latter also collaborating with similar financially motivated groups to scale their operations.
Package tracking text scams notwithstanding, Smishing Triad is also known to indulge in Magecart-like attacks that infect online shopping platforms with malicious code injections to intercept customer data.
“Smishing remains a rapidly evolving attack vector targeting consumers worldwide,” Resecurity said.
“The threat group’s tactics, techniques, and procedures combine two well-established methods: social engineering and the deployment of a phishing kit via iMessage. Since users tend to trust SMS and iMessage communication channels more than e-mail, this attack has successfully compromised numerous victims.”