Progress Software on Thursday disclosed a third vulnerability impacting its MOVEit Transfer application, as the Cl0p cybercrime gang deployed extortion tactics against affected companies.
The new flaw, which is yet to be assigned a CVE identifier, also concerns an SQL injection vulnerability that “could lead to escalated privileges and potential unauthorized access to the environment.”
The company is urging all its customers to disable all HTTP and HTTPs traffic to MOVEit Transfer on ports 80 and 443 to safeguard their environments while a patch is being prepared to address the weakness.
The revelation comes a week after Progress divulged another set of SQL injection vulnerabilities (CVE-2023-35036) that it said could be weaponized to access the application’s database content.
The vulnerabilities join CVE-2023-34362, which was exploited as a zero-day by the Clop ransomware gang in data theft attacks. Kroll said it found evidence that the group, dubbed Lace Tempest by Microsoft, had been testing the exploit as far back as July 2021.
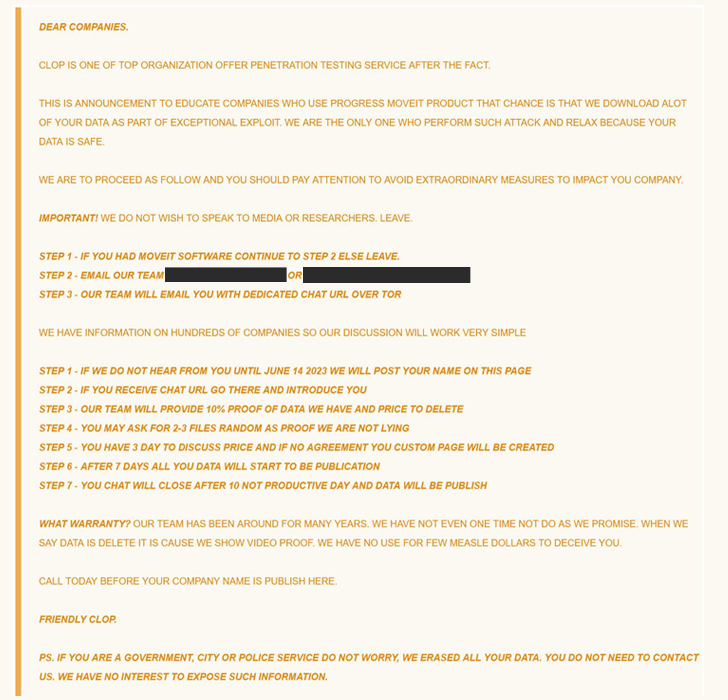
The development also coincides with the Cl0p actors listing the names of 27 companies that it claimed were hacked using the MOVEit Transfer flaw on its darknet leak portal. According to a report from CNN, this also includes multiple U.S. federal agencies such as the Department of Energy.
“The number of potentially breached organizations so far is significantly greater than the initial number named as part of Clop’s last MFT exploitation: the Fortra GoAnywhere MFT campaign,” ReliaQuest said.
???? Mastering API Security: Understanding Your True Attack Surface
Discover the untapped vulnerabilities in your API ecosystem and take proactive steps towards ironclad security. Join our insightful webinar!
Censys, a web-based search platform for assessing attack surface for internet-connected devices, said nearly 31% of over 1,400 exposed hosts running MOVEit are in the financial services industry, 16% in healthcare, 9% in information technology, and 8% in government and military sectors. Nearly 80% of the servers are based in the U.S.
Per Kaspersky’s analysis of 97 families spread via the malware-as-a-service (MaaS) business model between 2015 and 2022, ransomware leads with a 58% share, followed by information stealers (24%) and botnets, loaders, and backdoors (18%).
“Money is the root of all evil, including cybercrime,” the Russian cybersecurity company said, adding the MaaS schemes allow less technically proficient attackers to enter the fray, thereby lowering the bar for carrying out such attacks.