
Even though a lot of the functionality of domain controllers can be moved to the cloud, most organizations that use Active Directory need a hybrid infrastructure that gives users access to cloud resources (like OneDrive and Microsoft 365) through Azure Active Directory as well as on-premises file shares, printers and applications that still need local credentials.
Over the years, Microsoft has had multiple tools for managing hybrid identity and syncing cloud and on-premises users and groups.
SEE: Explore TechRepublic’s hybrid cloud cheat sheet.
Microsoft Identity Manager, which replaced Forefront Identity Manager, is supported until January 9, 2029, but its Azure AD Connector is deprecated. Azure AD Multi-Factor Authentication Server is also deprecated and will stop handling MFA requests after September 30, 2024. If you’re still using these tools, you will need to move to a newer option.
Jump to:
Azure AD Connect and its limitations
Azure AD Connect replaced the older DirSync and Azure AD Sync options for syncing users, groups and other directory objects to Azure AD. It supports:
- Password hash synchronization: Syncing a hash of each user’s AD password into Azure AD.
- Pass-through authentication: Sending users to Azure AD to sign in and then validating against AD, so they can use the same password in the cloud and for local resources without needing to set up federation.
- Active Directory Federation Services use.
But, Azure AD Connect requires setting up and maintaining a server on your network, and some of the requirements for running it don’t work for every organization, especially if you have multiple AD “forests,” which makes working with Azure AD complicated.
“To use it, you need to be in a connected forest; you need to have installed a database,” said Joseph Dadzie, a director in the Microsoft identity team. “That’s expensive to manage and deploy.
“We started getting feedback from a lot of customers around the cost of a deploying AD Connect sync and of maintaining it, and some feature gaps around if you are in a disconnected forest or you are in an organization where you are trying to do an M&A. So, we set out to look at ways to simplify it.”
Cloud sync aims to replace Azure AD Connect for cloud
The result is Azure AD Connect cloud sync, which started out as a tool for bringing identities from multiple disconnected AD forests into a single Azure AD tenant.
It still does that, but it’s now a lightweight alternative to AD Connect that doesn’t have quite as many features but is much faster to set up and requires fewer resources. This is because cloud sync moves much of the configuration into the cloud, needing only provisioning agents.
“When you look at AD Connect, almost all the configuration is done in the on-prem world, and it’s stored in that local server,” said Dadzie. “For cloud sync, the idea is to switch the configuration to be cloud based and have a very lightweight agent in the customer’s environment so that it’s easy to deploy.
“It takes about 10 megabytes, so you can have multiple of these working together for high availability solutions; something that’s more difficult to do if you have a full Connect sync capability.”
That high availability is particularly useful if you’re using Microsoft’s recommended password hash synchronization.
The future of cloud sync
Cloud sync can handle groups with up to 50,000 members, but it doesn’t cover everything you can do with AD Connect sync yet, Dadzie told us.
“If you’ve done a lot of customizations on attributes in your AD and you still use Exchange on-prem, there’s still some delta in the capabilities,” said Dadzie. “In the longer term, we will want to have it be the full replacement; we are not there yet.”
Currently, it can’t connect to LDAP directories and doesn’t yet have support for device objects, just users, groups and contacts. There are advanced customization and filtering options that aren’t available, and cloud sync can’t handle Exchange hybrid writeback, so you can’t use it for Exchange hybrid migrations.
Federation is supported but not Azure AD Domain Services or Pass Through Authentication, at least for disconnected forests. That’s something the AD Connect team is working on, Dadzie said, and writeback for security groups is also in development.
“Over the past year, we added the self-service password writeback scenarios,” said Dadzie.
Device writeback is also under development, because “almost any deployment starts with getting some of the users from on-prem to the cloud,” Dadzie notes. It’s slightly confusing because both Azure AS and Windows Hello For Business have services named Cloud Kerberos trust, which do different things, but Microsoft tells us the naming and documentation should become clearer in future.
The cloud sync team is also looking at alternatives to writeback.
“If you have an on-prem app and you have a cloud user who needs access to it, how do you give that user access without having an account in the on-prem AD,” said Dadzie. “We’re looking at what we might do in that space: Is there a way to have some of the secrets go down so that you can have the user credentials, where the user gets access to on-prem without having to have the user object in there?”
That’s still in the early stages, but there are regular updates to cloud sync functionality.
“Every quarter to six months, we update and add new capabilities,” said Dadzie. “We’re on a mission to chip away at the reasons why someone might still want to use the full AD Connect sync. We’re on a mission to keep adding to cloud sync to the point that we eventually replace AD Connect sync, but we are not there yet.”
Choosing between Azure AD Connect and cloud sync
There’s no urgency about moving to cloud sync if you need an AD Connect sync feature, but there are some scenarios where cloud sync is already the better choice, as well as less demanding.
“It works well for organizations that are not as complicated or don’t have a lot of objects; if they have less than 150K objects in their directory, then it’s easier to start off using cloud sync,” said Dadzie.
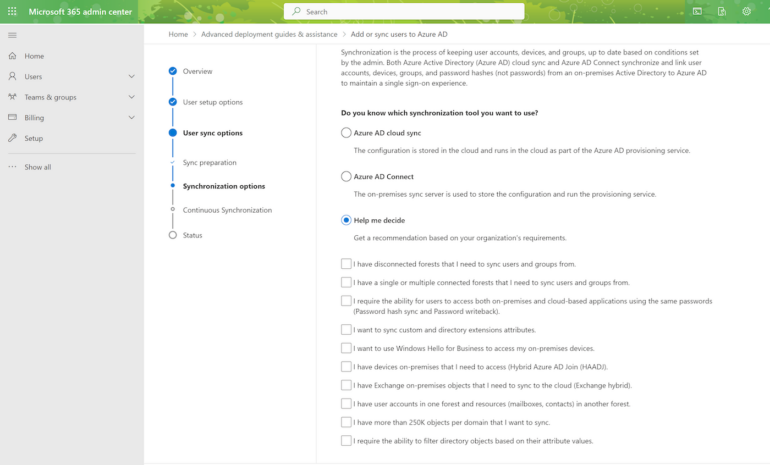
There’s a wizard in the Microsoft 365 admin center that walks you through choosing the right identity sync option as well as a step-by-step migration guide if you want to move from Azure AD Connect sync to cloud sync.
How complex that migration will be depends on how complex your AD environment is: “The more complex the environment is, then a more phased approach works,” Dazie said. But if your needs are less complex and you’re starting out with hybrid identity, he suggests starting with cloud sync for simplicity (Figure A).
Figure A
In fact, a big part of the appeal of cloud sync is that it’s designed to be much easier to get started with.
“In Connect sync, you have to do all the Schema Mapping yourself, whereas in cloud sync we try to autodiscover them for you, so you don’t have to hunt around and to make it easy for you to configure those,” said Dadzie. “The main philosophy we are trying to get with cloud sync is to make it super, super easy, so customers don’t have to think through these things.”
